Una conversazione con Terence Grey di Netscout Systems’ Fluke Networks Enterprise Solutions sulle tecniche di attacco e di difesa di una rete Wi-Fi oggi
Una conversazione con Terence Grey di Netscout Systems’ Fluke Networks Enterprise Solutions sulle tecniche di attacco e di difesa di una rete Wi-Fi oggi
How organisations can protect vulnerable wireless networks
Wi-Fi networks are inherently vulnerable, but there are steps organizations can take to protect themselves, according to Netscout Systems’ Fluke Networks Enterprise Solutions.
Netscout system engineer Terence Grey says, “If you have Wi-Fi, then you definitely have vulnerabilities. The point is to know what they are and have a solution in place so you know when you’re being attached, and can mitigate the risk and consequences.
“It’s no coincidence that security incidents are increasing at a faster rate than ever before and are costing organisations significantly more. These increases match the growth of the wireless industry: the more we have connected people on the web, the more we have security incidents.”
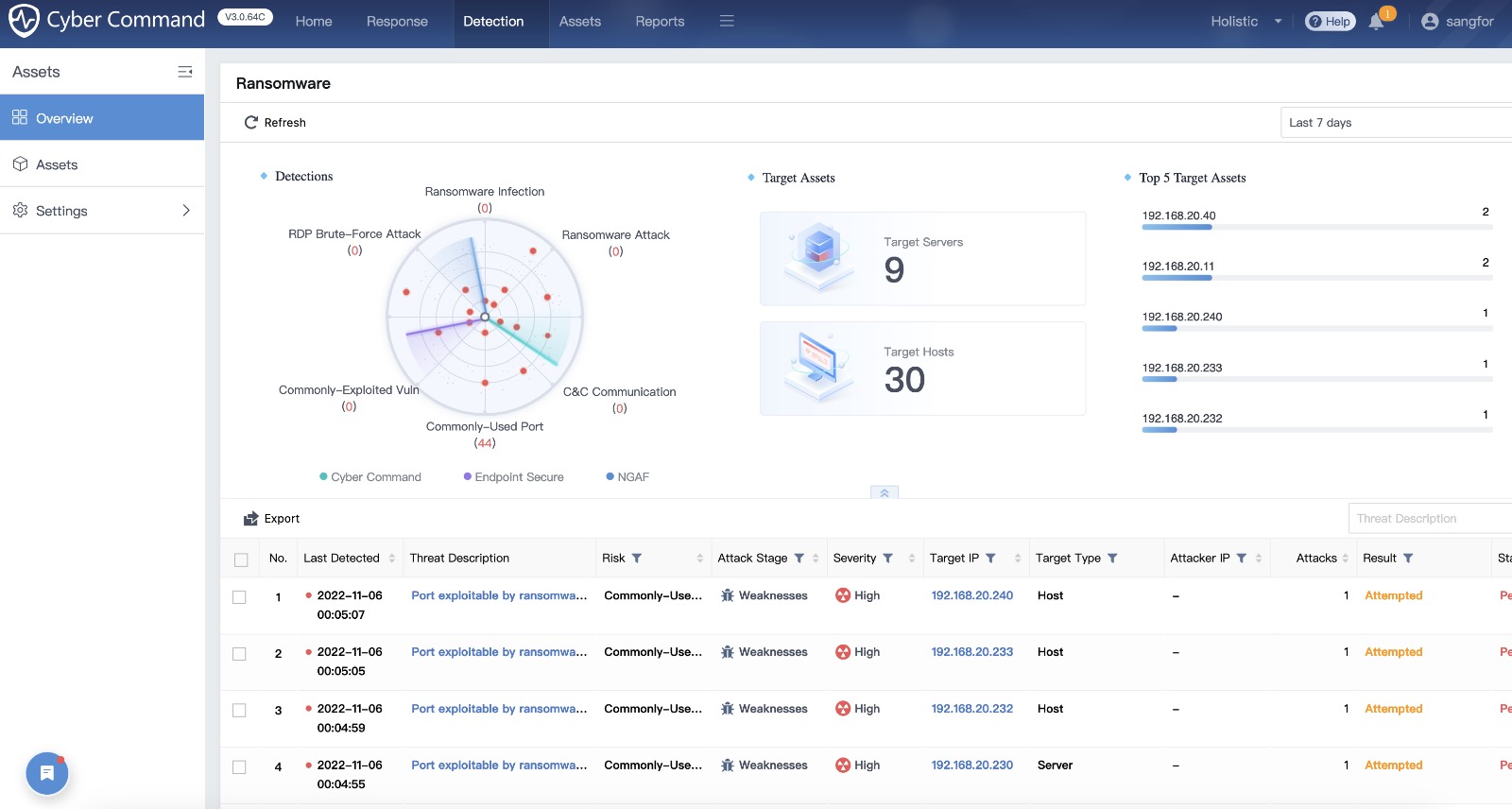
Netscout has identified the following four key attack vectors used to hack wireless networks:
1. Snooping: this attack vector is mostly undetectable as the attacker is just listening, usually using specialised equipment that is easily obtainable and cheap. It’s most effective against unencrypted networks and can become dangerous because the snooper can capture all of the company’s communications.
2. Denial of Service (DoS) attacks: this lets attackers disconnect a single wireless client or all wireless clients from an access point. These types of attacks have been around since the birth of the Internet. They are difficult to defend against. As well as denying access, they can also be used to redirect access to a so-called honeypot, which is an access point controlled by hackers.
3. Cracking: deducing or obtaining the wireless password lets hackers access your network. The best defence against this type of attack is to choose passwords that are long and include multiple types of different characters, numbers, and symbols.
4. Information theft: every mobile device is likely to connect to a wireless network at some point, in which case it will transmit different types of information. Hackers listen to this information, which may include systems access data or sensitive commercial information.
According to Grey, “If an attacker is trying to penetrate a company they’re not going to stick to a single method; they’re going to use multiple strategies. Wi-Fi is the lowest-hanging fruit, even if you have enterprise-level security in place.
“Keep in mind that the people protecting a network need to get it right all the time. A hacker only needs to get it right once, and they’re in. This makes it imperative for organisations to put strong security measures in place.”
 To minimise the risk of being attacked Netscout suggests the following five best practices:
To minimise the risk of being attacked Netscout suggests the following five best practices:
1. Start with a company security policy that specifically includes Wi-Fi.
2. Create an employee security awareness program and ensure every employee participates.
3. Practise safe networking with strong encryption and authentication, including client-side certificate validation.
4. Police the network with a wireless intrusion detection system (WIDS) or wireless intrusion protection system (WIPS).
5. Perform regular penetration testing to find out exactly where your vulnerabilities are so you can decide how to protect the organisation.
[Fonte: Facility Management (FM)]